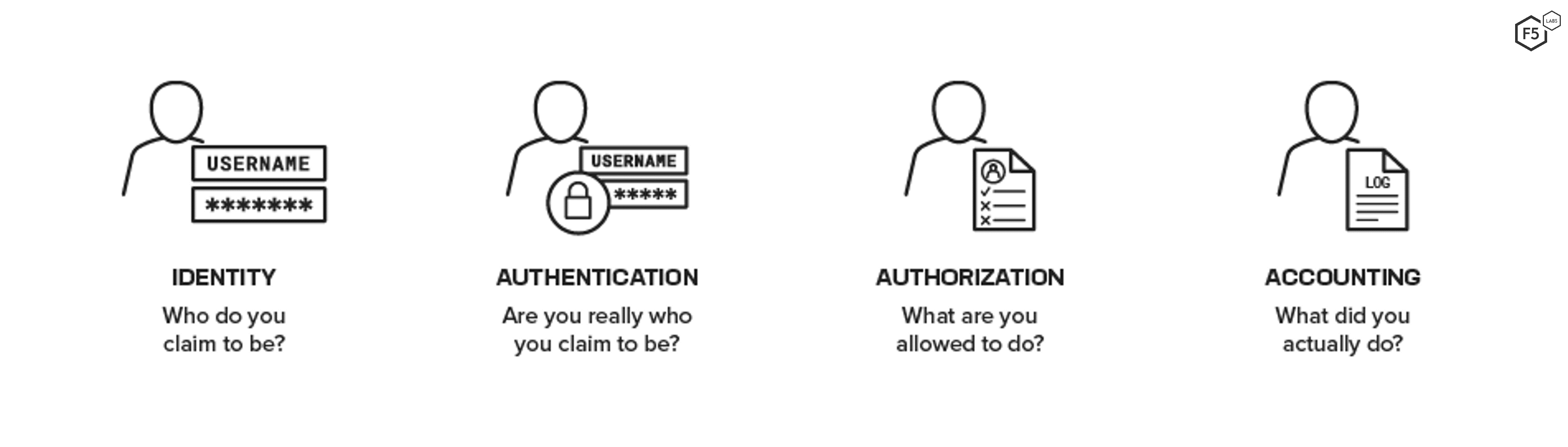
Free Course: Information Security - Authentication and Access Control from New York University (NYU) | Class Central
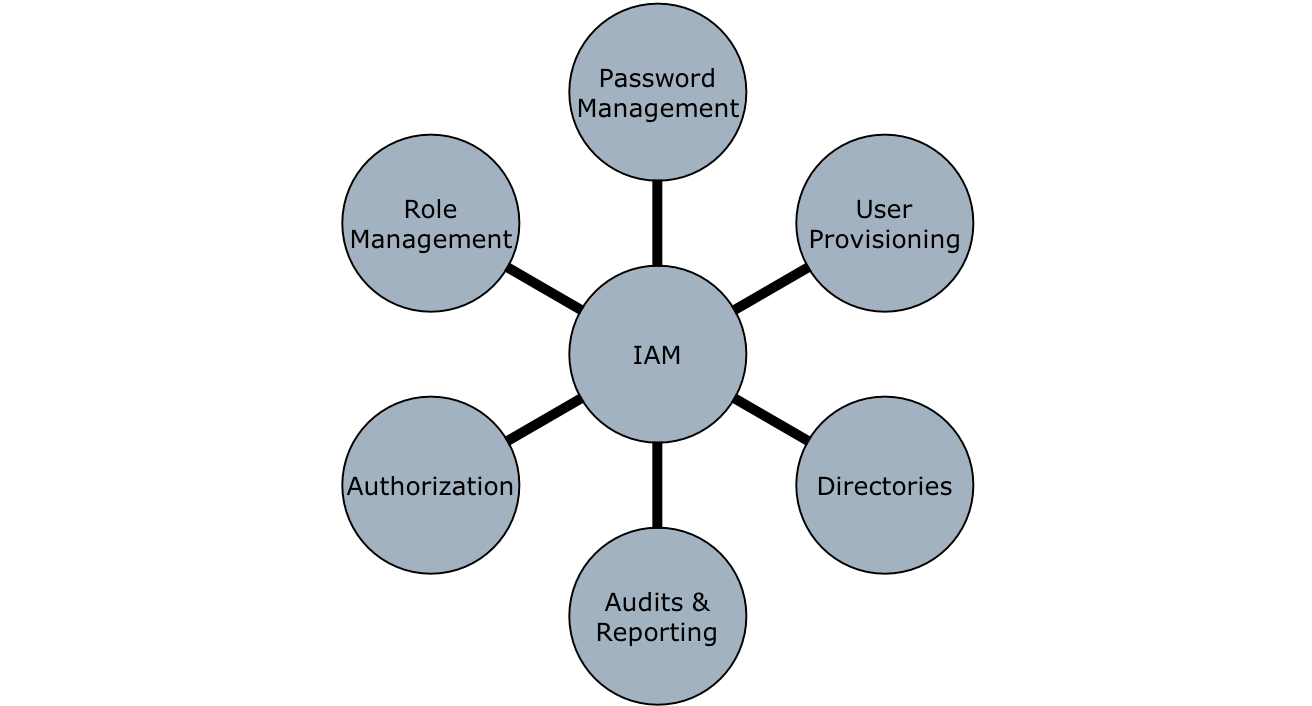
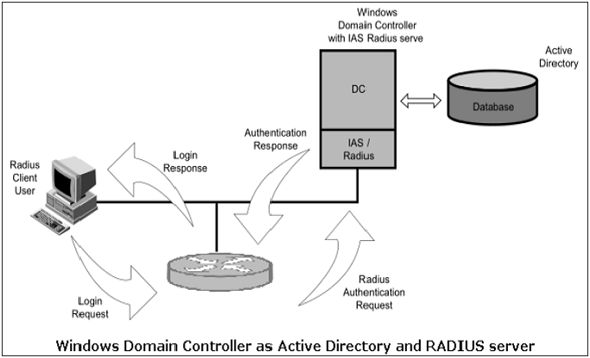
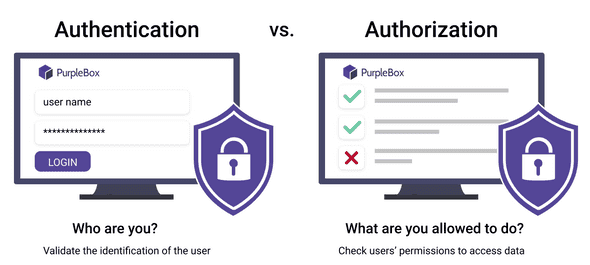
3 Basic A's of Identity and Access Management -Authentication, Authorization, and Accounting – Xorlogics
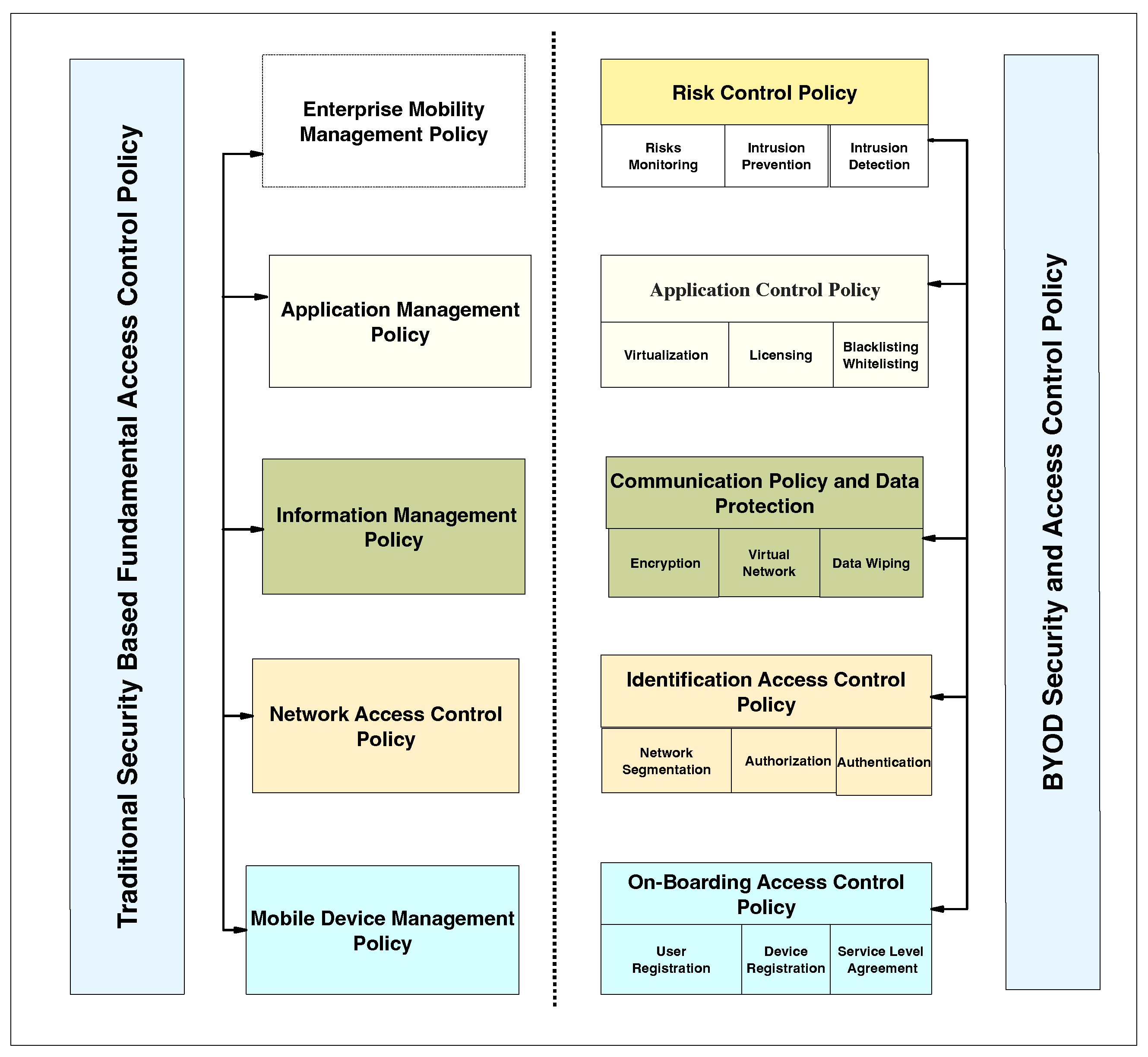
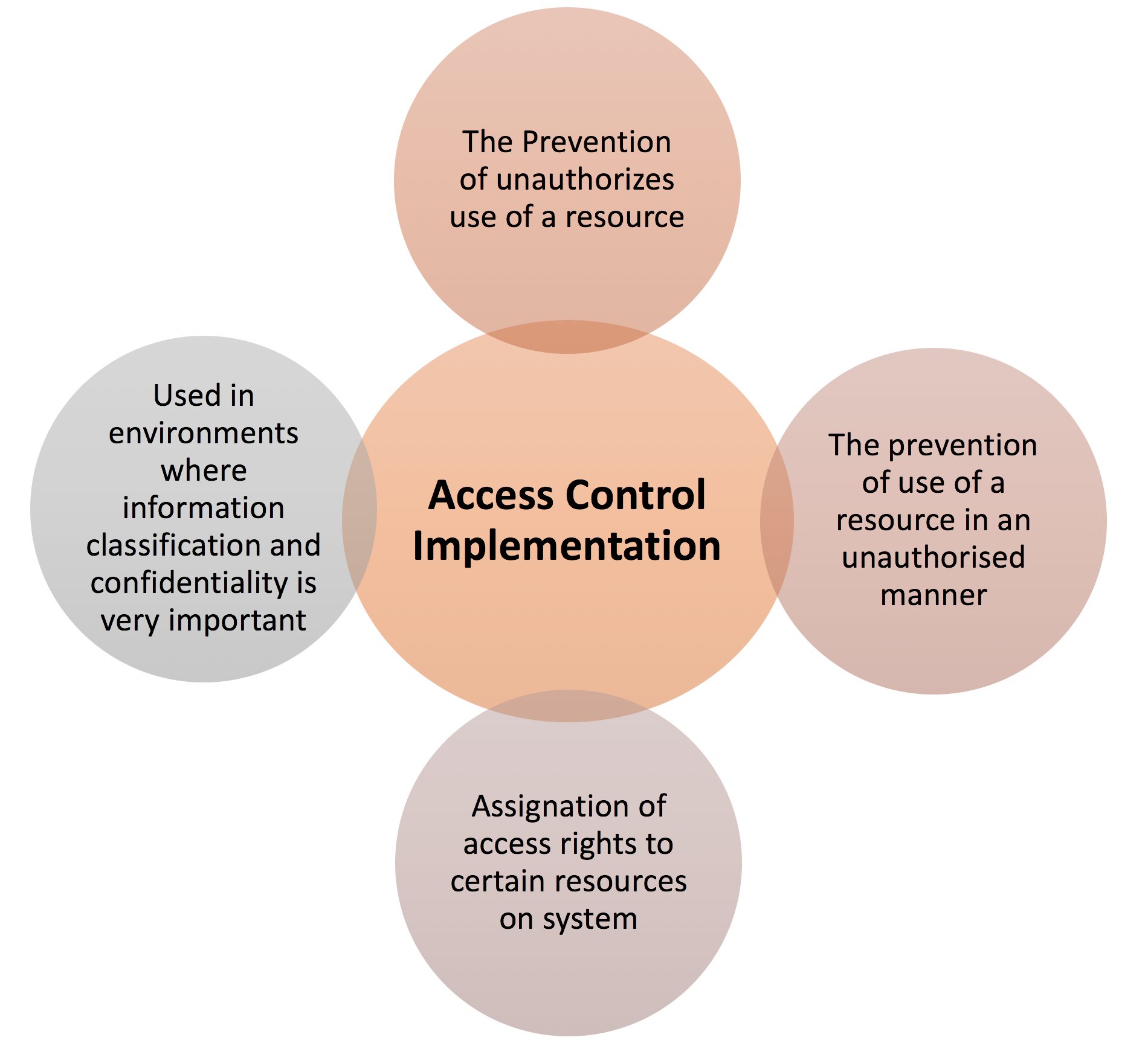
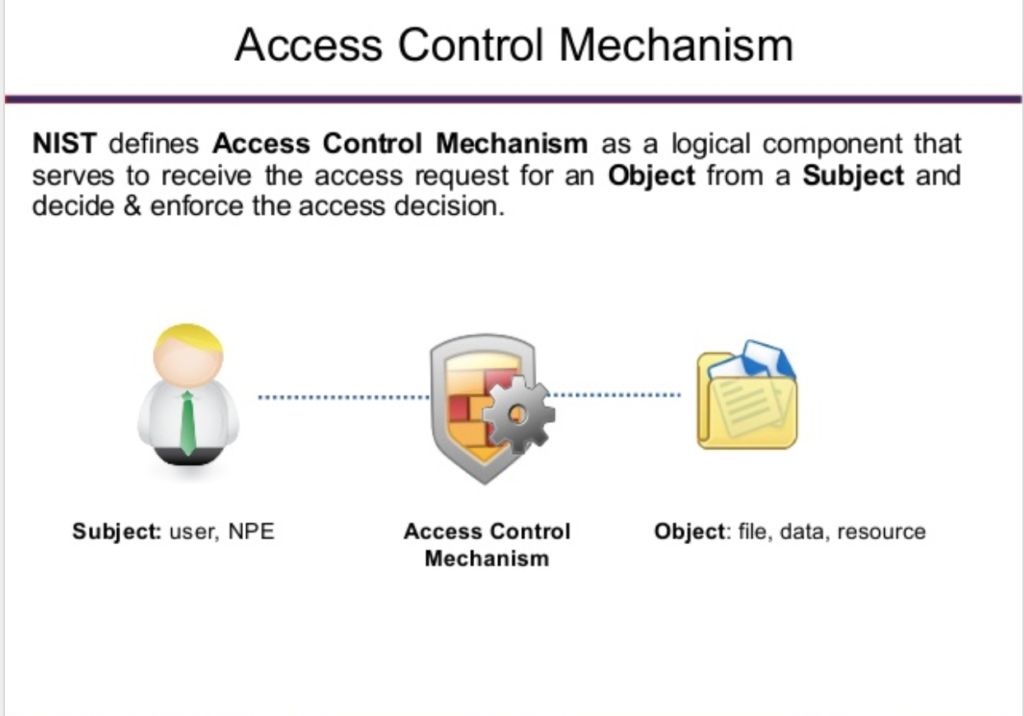
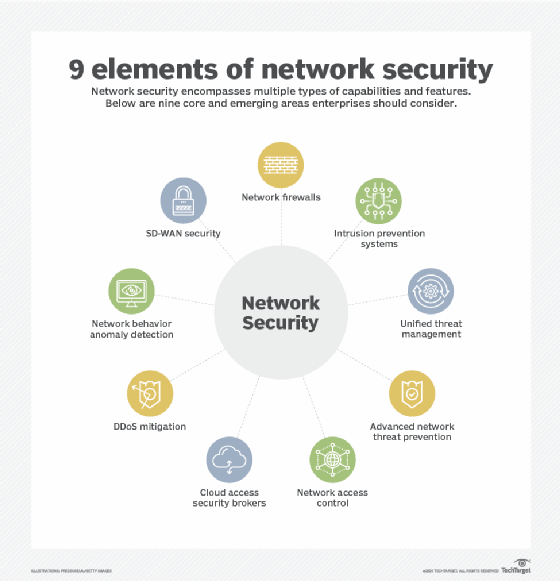
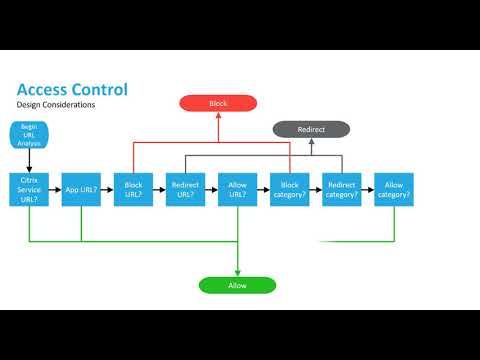
Applied Sciences | Free Full-Text | Systematic Literature Review on Security Access Control Policies and Techniques Based on Privacy Requirements in a BYOD Environment: State of the Art and Future Directions